On the internet today, our online accounts are exposed to a lot of risks. Leaked passwords from break-ins at major Internet properties or phishing attacks have lead to many account breaches. In order to protect my high-value accounts, I have either enabled two-factor authentication or I use federated sign-in, delegating to an account that has 2FA enabled (usually Google).
Recently, the FIDO industry association and the W3C have come up with WebAuthn, an open standard to promote passwordless sign-in using hardware tokens. If you run Android 7 or newer, you can use your phone as a token, and I have additionally bought a hardware Security Key from Yubikey to give this a try.
The idea behind the WebAuthn is relatively simple - it uses public-key cryptography for the client to authenticate itself (over TLS, of course). In a nutshell, the client creates a key pair and registers the public key with the server, while keeping the private key to itself. To authenticate, the server sends a challenge that the client signs using the private key. If the server is able to validate the signature with the previously stored public key, the client is considered authenticated.
Obviously, the hardware token must make sure the private key can never be extracted. Android phones use the built-in TPM module for that and hardware tokens have similar capabilities.
In order to try this out, I decided to use my tokens as a second factor for GitHub, replacing Google Authenticator with it's TOTP-based algorithm. I don't plan on using WebAuthn as a single factor - that is, without a password - for anything important, but it's nice having a standard that browsers support.
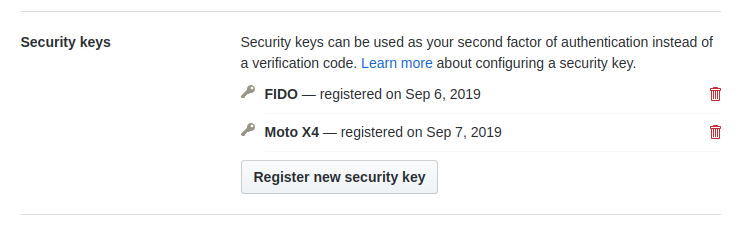
I got my Security Key working out of the box on Ubuntu 18.04.02 LTS without having to fiddle with udev rules. Chrome immediately supported it, I only had to plug it into the USB port. The process was straightforward via GitHub's 2FA configuration page (I had to switch the phone to desktop mode though). You can see both the Security Key and my phone registered:
When logging in, GitHub even lets you choose which second factor you want to use in case you still have TOTP enabled, for example. If you only have one device, don't forget to print the recovery codes! You don't want to lock yourself out of the account if you lose your phone or key. And generally, even if you use 2FA, make sure your recovery mechanisms aren't vulnerable to attacks (SMS comes to mind).
If you find out more about WebAuthn, check the WebAuthn Guide, or the fantastic Auth0's demo site, which gives you a look behind the scenes of the protocol.